My Favorite Things: Hardware Hacking and Reverse Engineering - Eclypsium
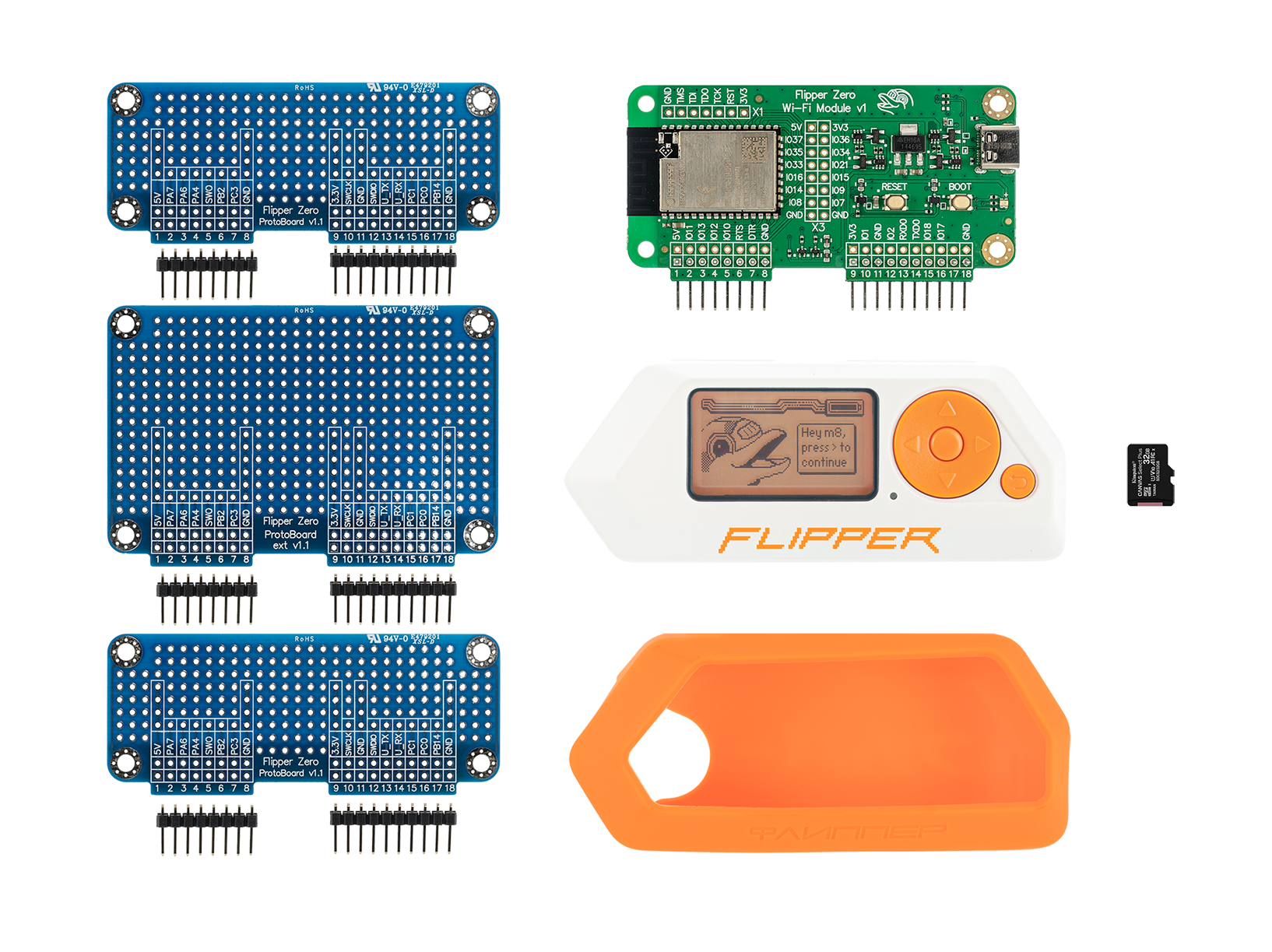
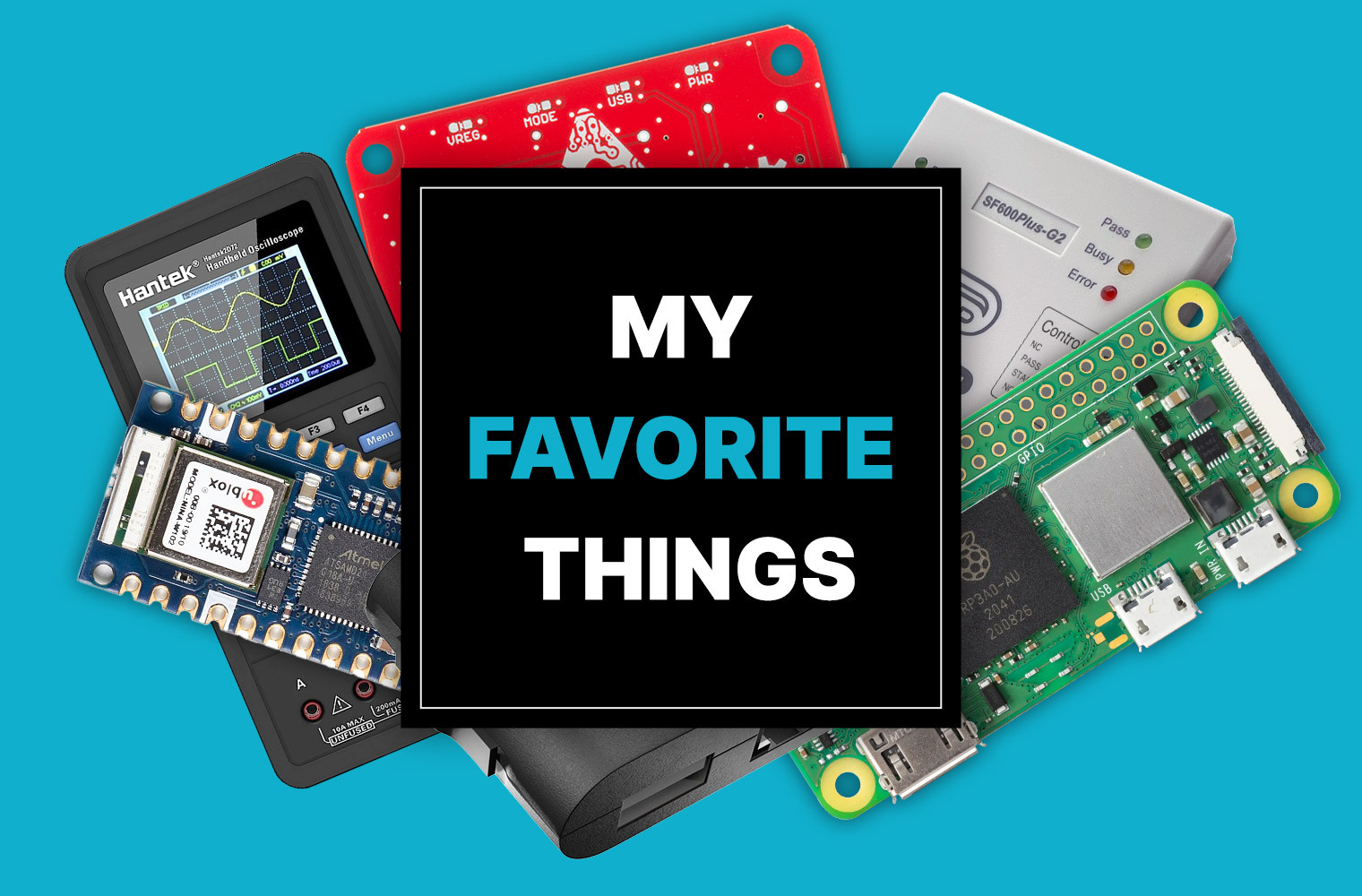
Favorite (Hacking) Things I really enjoy researching and acquiring “gadgets”. Recently, I spent a little time with Eclypsium’s research team discussing which hardware and software are most useful for security research, specifically hardware and firmware. The Eclypsium team has published extensive research in the past so I thought it would be excellent for the community […]

John Loucaides on Eclypsium's work with US government, Eclypsium, Inc. posted on the topic
Navigating the Cybersecurity Twitterverse 23 Influential Accounts to Follow in 2023 - SentinelOne

UPDATED] China Snuck A Tiny Microchip Inside US Top Secret Servers Used By The DoD And CIA — NSA Struggles To Assess Risk – Thomas J. Ackermann
TuxCare Blog - Insights and News on Linux Technology

Android TV Devices: Pre-0wned Supply Chain Security Threats - Eclypsium

HACKER DOUBLE SUMMER 2022 GUIDES — Part Four: ToorCamp, by DCG 201
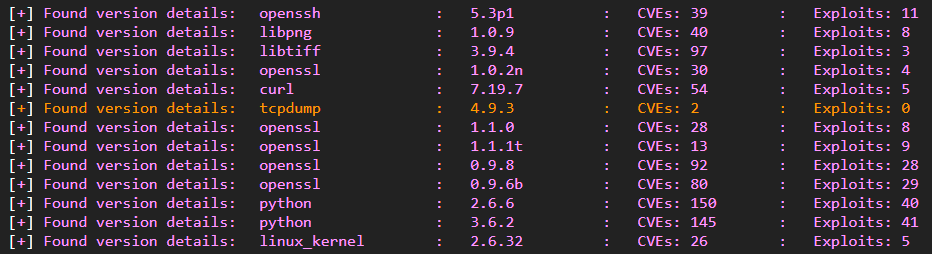
Flatlined: Analyzing Pulse Secure Firmware and Bypassing Integrity Checking - Eclypsium

Ajay (blue tick) (@IamAlch3mist) / X
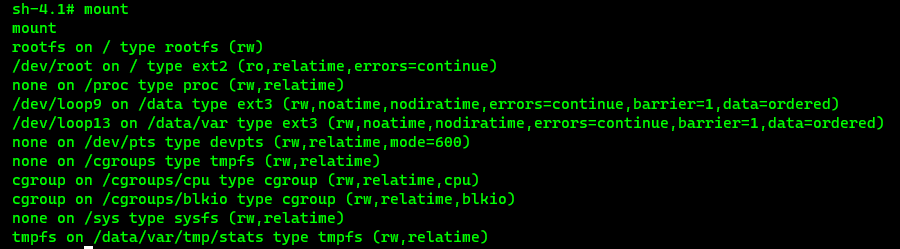
Flatlined: Analyzing Pulse Secure Firmware and Bypassing Integrity Checking - Malware News - Malware Analysis, News and Indicators

TryHackMe — Basic Malware RE Walkthrough, by Ravishanka Silva

Breaking the Chain of Trust
Malware Reverse Engineering for Beginners Explained